Global Warming: Fact or Fiction? Featuring Physicists Willie Soon and Elliott D. Bloom
Published: August 16, 2019
Is global warming real? Have any such predictions been established scientifically? Would massive “carbon” taxes and other controls put America and the world - especially the poor—at great risk?
At this special event, geoscientist and astrophysicist Willie Soon separates fact from fiction in the global warming debate. He explains why the forecasts from CO2 climate models have been so wrong and why solar influences on clouds, oceans, and wind drive climate change, not CO2 emissions. Stanford University physicist Elliott Bloom then comments.
“The whole point of science is to question accepted dogmas. For that reason, I respect Willie Soon as a good scientist and a courageous citizen.” - Freeman J. Dyson, Professor Emeritus of Physics, Institute for Advanced Study; Templeton Prize Laureate
“I am writing to express my deep admiration and respect for Dr. Willie Soon, a fine astrophysicist and human being.... As Willie has shown in many ways, observational facts do not fit the CO2 dogma, and an enormous amount of evidence points to the Sun as a much more important driver of climate.... Willie was right—whatever the cause of changing temperature, the main driver cannot be the concentration of atmospheric CO2.” - William Happer, Chairman, Presidential Committee on Climate Security; Cyrus Fogg Brackett Professor of Physics Emeritus, Princeton University; Member, National Academy of Sciences
Willie Soon is a geophysicist at the Harvard-Smithsonian Center for Astrophysics. He received his Ph.D. (with distinction) in aeronautical engineering from the University of Southern California, and he has been Astronomer at the Mount Wilson Observatory; Senior Scientist at the George C. Marshall Institute; Senior Visiting Fellow at the State Key Laboratory of Marine Environmental Science at Xiamen University; and Professor of Environmental Studies at the University of Putra Malaysia. The author of 90 scientific papers, he has IEEE received the Nuclear & Plasma Sciences Society Award, Rockwell Dennis Hunt Award, Smithsonian Institution Award, Courage in Defense of Science Award, Petr Beckmann Award for Courage and Achievement in Defense of Scientific Truth and Freedom, and Frederick Seitz Memorial Award.
Elliott D. Bloom is Professor Emeritus in the Kavli Institute for Particle Astrophysics and Cosmology at the Stanford Linear Accelerator Laboratory (SLAC) at Stanford University and a Fellow of the American Physical Society. He was a member of the SLAC team with Jerome I. Friedman, Henry W. Kendall and Richard E. Taylor who received the Nobel Prize in Physics.
The Independent Institute is a non-profit, non-partisan, public-policy research and educational organization that shapes ideas into profound and lasting impact. The mission of Independent is to boldly advance peaceful, prosperous, and free societies grounded in a commitment to human worth and dignity. Applying independent thinking to issues that matter, the Independent Institute creates transformational ideas for today’s most pressing social and economic challenges. By connecting these ideas with other organizations and networks, Independent seeks to inspire action that can unleash an era of unparalleled human flourishing at home and around the globe. http://www.independent.org/publicatio...
2014 Breaks Heat Record, Challenging Global Warming Skeptics
- By JUSTIN GILLIS - JAN. 16, 2015 - The New York Times
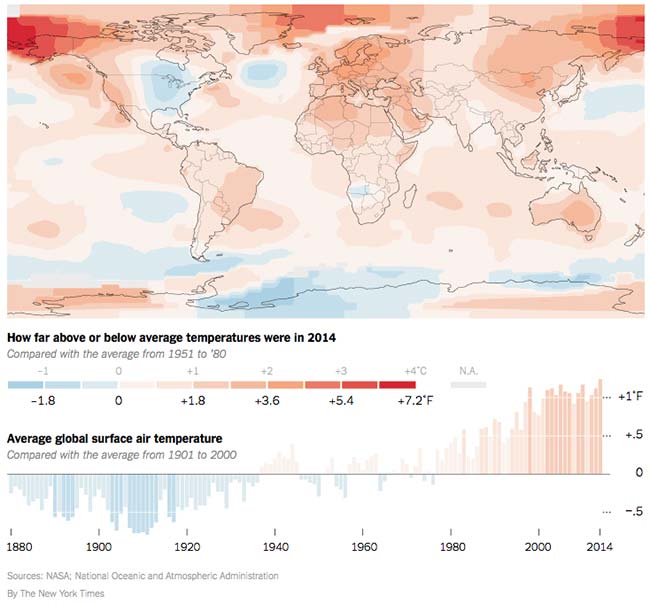
Last year was the hottest on earth since record-keeping began in 1880, scientists reported on Friday, underscoring warnings about the risks of runaway greenhouse gas emissions and undermining claims by climate change contrarians that global warming had somehow stopped.
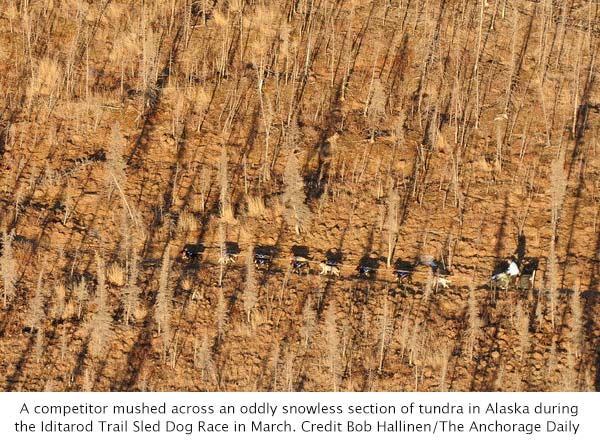
Extreme heat blanketed Alaska and much of the western United States last year. Records were set across large areas of every inhabited continent. And the ocean surface was unusually warm virtually everywhere except near Antarctica, the scientists said, providing the energy that fueled damaging Pacific storms.
In the annals of climatology, 2014 surpassed 2010 as the warmest year. The 10 warmest years have all occurred since 1997, a reflection of the relentless planetary warming that scientists say is a consequence of human activity and poses profound long-term risks to civilization and nature.
“Climate change is perhaps the major challenge of our generation,” said Michael H. Freilich, director of earth sciences at NASA, one of the agencies that track global temperatures.
Of the large land areas where many people live, only the eastern portion of the United States recorded below-average temperatures in 2014, in sharp contrast to the unusual heat in the West. Some experts think the weather pattern that produced those American extremes is an indirect consequence of the release of greenhouse gases, though that is not proven.
Several scientists said the most remarkable thing about the 2014 record was that it had occurred in a year that did not feature a strong El Niño, a large-scale weather pattern in which the Pacific Ocean pumps an enormous amount of heat into the atmosphere.
Skeptics of climate change have long argued that global warming stopped around 1998, when an unusually powerful El Niño produced the hottest year of the 20th century. Some politicians in Washington have seized on that claim to justify inaction on emissions.
But the temperature of 1998 is now being surpassed every four or five years, and 2014 was the first time that happened without a significant El Niño. Gavin A. Schmidt, head of NASA’s Goddard Institute for Space Studies in Manhattan, said the next strong El Niño would probably rout all temperature records.
“Obviously, a single year, even if it is a record, cannot tell us much about climate trends,” said Stefan Rahmstorf, head of earth system analysis at the Potsdam Institute for Climate Impact Research in Germany. “However, the fact that the warmest years on record are 2014, 2010 and 2005 clearly indicates that global warming has not ‘stopped in 1998,’ as some like to falsely claim.”
Such claims are unlikely to go away, though. John R. Christy, an atmospheric scientist at the University of Alabama in Huntsville who is known for his skepticism about the seriousness of global warming, pointed out in an interview that 2014 had surpassed the other record-warm years by only a few hundredths of a degree, well within the error margin of global temperature measurements. “Since the end of the 20th century, the temperature hasn’t done much,” Dr. Christy said. “It’s on this kind of warmish plateau.”
Despite such arguments from a handful of scientists, the vast majority of those who study the climate say the earth is in a long-term warming trend that is profoundly threatening and caused almost entirely by human activity.
The Warmest Year on Record
Parts of the eastern United States were cooler than average last year, but globally 2014 was the warmest year in recorded history.
They expect the heat to get much worse over coming decades, but already it is killing forests around the world, driving plants and animals to extinction, melting land ice and causing the seas to rise at an accelerating pace.
“It is exceptionally unlikely that we would be witnessing a record year of warmth, during a record-warm decade, during a several decades-long period of warmth that appears to be unrivaled for more than a thousand years, were it not for the rising levels of planet-warming gases produced by the burning of fossil fuels,” Michael E. Mann, a climate scientist at the Pennsylvania State University, said in an email.
NASA and the other American agency that maintains long-term temperature records, the National Oceanic and Atmospheric Administration, issued separate data compilations on Friday that confirmed the 2014 record. A Japanese agency had released preliminary information in early January showing 2014 as the warmest year.
One more scientific group, in Britain, that curates the world’s temperature record is scheduled to report in the coming weeks.
Separate temperature measurements taken from satellites do not show 2014 as a record year, although it is close. Several scientists said the satellite readings reflected temperatures in the atmosphere, not at the earth’s surface, so it was not surprising that they would differ slightly from the ground and ocean-surface measurements that showed record warmth.
“Why do we keep getting so many record-warm years?” Dr. Schmidt asked in an interview. “It’s because the planet is warming. The basic issue is the long-term trend, and it is not going away.”
February 1985 was the last time global surface temperatures fell below the 20th-century average for a given month, meaning that no one younger than 30 has ever lived through a below-average month. The last full year that was colder than the 20th-century average was 1976.
The contiguous United States set a temperature record in 2012, a year of scorching heat waves and drought. But, mostly because of the unusual chill in the East, 2014 was only the 34th warmest year on record for the lower 48 states.
That cold was drawn into the interior of the country by a loop in a current called the jet stream that allowed Arctic air to spill southward. But an offsetting kink allowed unusually warm tropical air to settle over the West, large parts of Alaska and much of the Arctic.
A few recent scientific papers say that such long-lasting kinks in the jet stream have become more likely because global warming is rapidly melting the sea ice in the Arctic, but many leading scientists are not convinced on that point.
Whatever the underlying cause, last year’s extreme warmth in the West meant that Alaska, Arizona, California and Nevada all set temperature records. Some parts of California essentially had no winter last year, with temperatures sometimes running 10 to 15 degrees above normal for the season. The temperature in Anchorage, Alaska’s largest city, never fell below zero in 2014, the first time that has happened in 101 years of record-keeping for the city.
Twenty years of global negotiations aimed at slowing the growth of heat-trapping emissions have yielded little progress. However, 2014 saw signs of large-scale political mobilization on the issue, as more than 300,000 people marched in New York City in September, and tens of thousands more took to the streets in other cities around the world.
The next big attempt at a global climate agreement will come when negotiators from around the world gather in Paris in December. Political activists on climate change wasted no time Friday in citing the 2014 heat record as proof that strong action was needed.
“The steady and now record-breaking rise in average global temperatures is not an issue for another day,” Michael R. Bloomberg, the former New York mayor who is spending tens of millions of dollars of his personal fortune to battle climate change, said in a statement. “It’s a clear and present danger that poses major economic, health, environmental and geopolitical risks.”
Also see: https://venusproject.org/exposed/climate-change-theory.html
Ocean Life Faces Mass Extinction, Broad Study Says
- By Carl Zimmer - January 15, 2015 - The New York Times
A team of scientists, in a groundbreaking analysis of data from hundreds of sources, has concluded that humans are on the verge of causing unprecedented damage to the oceans and the animals living in them.
“We may be sitting on a precipice of a major extinction event,” said Douglas J. McCauley, an ecologist at the University of California, Santa Barbara, and an author of the new research, which was published on Thursday in the journal Science.
But there is still time to avert catastrophe, Dr. McCauley and his colleagues also found. Compared with the continents, the oceans are mostly intact, still wild enough to bounce back to ecological health.
“We’re lucky in many ways,” said Malin L. Pinsky, a marine biologist at Rutgers University and another author of the new report. “The impacts are accelerating, but they’re not so bad we can’t reverse them.”
Scientific assessments of the oceans’ health are dogged by uncertainty: It’s much harder for researchers to judge the well-being of a species living underwater, over thousands of miles, than to track the health of a species on land. And changes that scientists observe in particular ocean ecosystems may not reflect trends across the planet.
Dr. Pinsky, Dr. McCauley and their colleagues sought a clearer picture of the oceans’ health by pulling together data from an enormous range of sources, from discoveries in the fossil record to statistics on modern container shipping, fish catches and seabed mining. While many of the findings already existed, they had never been juxtaposed in such a way.
A number of experts said the result was a remarkable synthesis, along with a nuanced and encouraging prognosis.
“I see this as a call for action to close the gap between conservation on land and in the sea,” said Loren McClenachan of Colby College, who was not involved in the study.
There are clear signs already that humans are harming the oceans to a remarkable degree, the scientists found. Some ocean species are certainly overharvested, but even greater damage results from large-scale habitat loss, which is likely to accelerate as technology advances the human footprint, the scientists reported.
Coral reefs, for example, have declined by 40 percent worldwide, partly as a result of climate-change-driven warming.
Some fish are migrating to cooler waters already. Black sea bass, once most common off the coast of Virginia, have moved up to New Jersey. Less fortunate species may not be able to find new ranges. At the same time, carbon emissions are altering the chemistry of seawater, making it more acidic.
“If you cranked up the aquarium heater and dumped some acid in the water, your fish would not be very happy,” Dr. Pinsky said. “In effect, that’s what we’re doing to the oceans.”
Fragile ecosystems like mangroves are being replaced by fish farms, which are projected to provide most of the fish we consume within 20 years. Bottom trawlers scraping large nets across the sea floor have already affected 20 million square miles of ocean, turning parts of the continental shelf to rubble. Whales may no longer be widely hunted, the analysis noted, but they are now colliding more often as the number of container ships rises.
Mining operations, too, are poised to transform the ocean. Contracts for seabed mining now cover 460,000 square miles underwater, the researchers found, up from zero in 2000. Seabed mining has the potential to tear up unique ecosystems and introduce pollution into the deep sea.
The oceans are so vast that their ecosystems may seem impervious to change. But Dr. McClenachan warned that the fossil record shows that global disasters have wrecked the seas before. “Marine species are not immune to extinction on a large scale,” she said.
Until now, the seas largely have been spared the carnage visited on terrestrial species, the new analysis also found.
The fossil record indicates that a number of large animal species became extinct as humans arrived on continents and islands. For example, the moa, a giant bird that once lived on New Zealand, was wiped out by arriving Polynesians in the 1300s, probably within a century.
But it was only after 1800, with the Industrial Revolution, that extinctions on land really accelerated.
Humans began to alter the habitat that wildlife depended on, wiping out forests for timber, plowing under prairie for farmland, and laying down roads and railroads across continents.
Species began going extinct at a much faster pace. Over the past five centuries, researchers have recorded 514 animal extinctions on land. But the authors of the new study found that documented extinctions are far rarer in the ocean.
Before 1500, a few species of seabirds are known to have vanished. Since then, scientists have documented only 15 ocean extinctions, including animals such as the Caribbean monk seal and the Steller’s sea cow.
While these figures are likely underestimates, Dr. McCauley said that the difference was nonetheless revealing.
“Fundamentally, we’re a terrestrial predator,” he said. “It’s hard for an ape to drive something in the ocean extinct.”
Many marine species that have become extinct or are endangered depend on land — seabirds that nest on cliffs, for example, or sea turtles that lay eggs on beaches.
Still, there is time for humans to halt the damage, Dr. McCauley said, with effective programs limiting the exploitation of the oceans. The tiger may not be salvageable in the wild — but the tiger shark may well be, he said.
“There are a lot of tools we can use,” he said. “We better pick them up and use them seriously.”
Dr. McCauley and his colleagues argue that limiting the industrialization of the oceans to some regions could allow threatened species to recover in other ones. “I fervently believe that our best partner in saving the ocean is the ocean itself,” said Stephen R. Palumbi of Stanford University, an author of the new study.
The scientists also argued that these reserves had to be designed with climate change in mind, so that species escaping high temperatures or low pH would be able to find refuge.
“It’s creating a hopscotch pattern up and down the coasts to help these species adapt,” Dr. Pinsky said.
Ultimately, Dr. Palumbi warned, slowing extinctions in the oceans will mean cutting back on carbon emissions, not just adapting to them.
“If by the end of the century we’re not off the business-as-usual curve we are now, I honestly feel there’s not much hope for normal ecosystems in the ocean,” he said. “But in the meantime, we do have a chance to do what we can. We have a couple decades more than we thought we had, so let’s please not waste it.”
The Evil Millionaire Mullahs
- By Paul Klebnikov, July 21, 2003
 A looming nuclear threat to the rest of the world, Iran is robbing its own people of prosperity. But the ruling mullahs at the top are getting extremely rich.
A looming nuclear threat to the rest of the world, Iran is robbing its own people of prosperity. But the ruling mullahs at the top are getting extremely rich.
It's rumble time in Tehran. At dozens of intersections in the capital of Iran thousands of students are protesting on a recent Friday around midnight, as they do nearly every night, chanting pro-democracy slogans and lighting bonfires on street corners. Residents of the surrounding middle-class neighborhoods converge in their cars, honking their horns in raucous support.
Suddenly there's thunder in the air. A gang of over 30 motorcyclists, brandishing iron bars and clubs, roars through the stalled traffic. They glare at the drivers, yell threats, thump cars. Burly and bearded, the bikers yank two men from their auto and pummel them. Most protesters scatter. Uniformed policemen watch impassively as the thugs beat the last stragglers.
These bikers are part of the Hezbollah militia, recruited mostly from the countryside. Iran's ruling mullahs roll them out whenever they need to intimidate their opponents. The Islamic Republic is a strange dictatorship. As it moves to repress growing opposition to clerical rule, the regime relies not on soldiers or uniformed police (many of whom sympathize with the protesters) but on the bullies of Hezbollah and the equally thuggish Revolutionary Guards. The powers that be claim to derive legitimacy from Allah but remain on top with gangsterlike methods of intimidation, violence and murder.
Who controls today's Iran? Certainly not Mohammad Khatami, the twice-elected moderate president, or the reformist parliament. Not even the Supreme Leader Ayatollah Ali Khamenei--a stridently anti-American but unremarkable cleric plucked from the religious ranks 14 years ago to fill the shoes of his giant predecessor, Ayatollah Khomeini--is fully in control. The real power is a handful of clerics and their associates who call the shots behind the curtain and have gotten very rich in the process.
The economy bears more than a little resemblance to the crony capitalism that sprouted from the wreck of the Soviet Union. The 1979 revolution expropriated the assets of foreign investors and the nation's wealthiest families; oil had long been nationalized, but the mullahs seized virtually everything else of value--banks, hotels, car and chemical companies, makers of drugs and consumer goods. What distinguishes Iran is that many of these assets were given to Islamic charitable foundations, controlled by the clerics. According to businessmen and former foundation executives, the charities now serve as slush funds for the mullahs and their supporters.
Iran has other lethal secrets besides its nuclear program, now the subject of prying international eyes. Dozens of interviews with businessmen, merchants, economists and former ministers and other top government officials reveal a picture of a dictatorship run by a shadow government that--the U.S. State Department suspects--finances terrorist groups abroad through a shadow foreign policy. Its economy is dominated by shadow business empires and its power is protected by a shadow army of enforcers.
Ironically, the man most adept at manipulating this hidden power structure is one of Iran's best-known characters--Ali Akbar Hashemi Rafsanjani, who has been named an ayatollah, or religious leader. He was the speaker of parliament and Khomeini's right-hand man in the 1980s, president of Iran from 1989 to 1997 and is now chairman of the powerful Expediency Council, which resolves disputes between the clerical establishment and parliament. Rafsanjani has more or less run the Islamic Republic for the past 24 years.
He played it smart, aligning himself in the 1960s with factions led by Ayatollah Khomeini, then becoming the go-to guy after the revolution. A hard-liner ideologically, Rafsanjani nonetheless has a pragmatic streak. He convinced Khomeini to end the Iran-Iraq war and broke Iran's international isolation by establishing trade relations with the Soviet Union, China, Saudi Arabia and the United Arab Emirates. In the 1990s he restarted Iran's nuclear program.
He is also the father of Iran's "privatization" program. During his presidency the stock market was revived, some government companies were sold to insiders, foreign trade was liberalized and the oil sector was opened up to private companies. Most of the good properties and contracts, say dissident members of Iran's Chamber of Commerce, ended up in the hands of mullahs, their associates and, not least, Rafsanjani's family, who rose from modest origins as pistachio farmers. "They were not rich people, so they worked hard and always tried to help their relatives get ahead," remembers Reza, a historian who declines to use his last name and who studied with one of Rafsanjani's brothers at Tehran University in the early 1970s. "When they were in university, two brothers earned money on the side tutoring theological students and preparing their exam papers."
The 1979 revolution transformed the Rafsanjani clan into commercial pashas. One brother headed the country's largest copper mine; another took control of the state-owned TV network; a brother-in-law became governor of Kerman province, while a cousin runs an outfit that dominates Iran's $400 million pistachio export business; a nephew and one of Rafsanjani's sons took key positions in the Ministry of Oil; another son heads the Tehran Metro construction project (an estimated $700 million spent so far). Today, operating through various foundations and front companies, the family is also believed to control one of Iran's biggest oil engineering companies, a plant assembling Daewoo automobiles, and Iran's best private airline (though the Rafsanjanis insist they do not own these assets).
None of this sits well with the populace, whose per capita income is $1,800 a year. The gossip on the street, going well beyond the observable facts, has the Rafsanjanis stashing billions of dollars in bank accounts in Switzerland and Luxembourg; controlling huge swaths of waterfront in Iran's free economic zones on the Persian Gulf; and owning whole vacation resorts on the idyllic beaches of Dubai, Goa and Thailand.
But not much of the criticism makes its way into print. One journalist who dared to investigate Rafsanjani's secret dealings and his alleged role in extrajudicial killings of dissidents is now languishing in jail. He's lucky. Iranian politics can be deadly. Five years ago Tehran was rocked by murders of journalists and anticorruption activists; some were beheaded, others mutilated.
Some of the family's wealth is out there for all to see. Rafsanjani's youngest son, Yaser, owns a 30-acre horse farm in the superfashionable Lavasan neighborhood of north Tehran, where land goes for over $4 million an acre. Just where did Yaser get his money? A Belgian-educated businessman, he runs a large export-import firm that includes baby food, bottled water and industrial machinery.
Until a few years ago the simplest way to get rich quick was through foreign-currency trades. Easy, if you could get greenbacks at the subsidized import rate of 1,750 rials to the dollar and resell them at the market rate of 8,000 to the dollar. You needed only the right connections for an import license. "I estimate that, over a period of ten years, Iran lost $3 billion to $5 billion annually from this kind of exchange-rate fraud," says Saeed Laylaz, an economist, now with Iran's biggest carmaker. "And the lion's share of that went to about 50 families."
One of the families benefiting from the foreign trade system was the Asgaroladis, an old Jewish clan of bazaar traders, who converted to Islam several generations ago. Asadollah Asgaroladi exports pistachios, cumin, dried fruit, shrimp and caviar, and imports sugar and home appliances; his fortune is estimated by Iranian bankers to be some $400 million. Asgaroladi had a little help from his older brother, Habibollah, who, as minister of commerce in the 1980s, was in charge of distributing lucrative foreign-trade licenses. (He was also a counterparty to commodities trader and then-fugitive Marc Rich, who helped Iran bypass U.S.-backed sanctions.)
The other side of Iran's economy belongs to the Islamic foundations, which account for 10% to 20% of the nation's GDP--$115 billion last year. Known as bonyads, the best-known of these outfits were established from seized property and enterprises by order of Ayatollah Khomeini in the first weeks of his regime. Their mission was to redistribute to the impoverished masses the "illegitimate" wealth accumulated before the revolution by "apostates" and "blood-sucking capitalists." And, for a decade or so, the foundations shelled out money to build low-income housing and health clinics. But since Khomeini's death in 1989 they have increasingly forsaken their social welfare functions for straightforward commercial activities.
Until recently they were exempt from taxes, import duties and most government regulation. They had access to subsidized foreign currency and low-interest loans from state-owned banks. And they were not accountable to the Central Bank, the Ministry of Finance or any other government institution. Formally, they are under the jurisdiction of the Supreme Leader; effectively, they operate without any oversight, answerable only to Allah.
According to Shiite Muslim tradition, devout businessmen are expected to donate 20% of profits to their local mosques, which use the money to help the poor. By contrast, many bonyads seem like rackets, extorting money from entrepreneurs. Besides the biggest national outfits, almost every Iranian town has its own bonyad, affiliated with local mullahs. "Many small businessmen complain that as soon as you start to make some money, the leading mullah will come to you and ask for a contribution to his local charity," says an opposition economist, who declines to give his name. "If you refuse, you will be accused of not being a good Muslim. Some witnesses will turn up to testify that they heard you insult the Prophet Mohammad, and you will be thrown in jail."
Other charities resemble multinational conglomerates. The Mostazafan & Jambazan Foundation (Foundation for the Oppressed and War Invalids) is the second-largest commercial enterprise in the country, behind the state-owned National Iranian Oil Co. Until recently it was run by a man named Mohsen Rafiqdoost. The son of a vegetable-and-fruit merchant at the Tehran bazaar, Rafiqdoost got his big break in 1979, when he was chosen to drive Ayatollah Khomeini from the airport after his triumphal return from exile in Paris.
Khomeini made him Minister of the Revolutionary Guards to quash internal dissent and smuggle in weapons for the Iran-Iraq war. In 1989, when Rafsanjani became president, Rafiqdoost gained control of the Mostazafan Foundation, which employs up to 400,000 workers and has assets that in all probability exceed $10 billion.
Theoretically the Mostazafan Foundation is a social welfare organization. By 1996 it began taking government funds to cover welfare disbursements; soon it plans to spin off its social responsibilities altogether, leaving behind a purely commercial conglomerate owned by--whom? That is not clear. Why does this foundation exist? "I don't know--ask Mr. Rafiqdoost," says Abbas Maleki, a foreign policy adviser to Ayatollah Rafsanjani.
A picture emerges from one Iranian businessman who used to handle the foreign trade deals for one of the big foundations. Organizations like the Mostazafan serve as giant cash boxes, he says, to pay off supporters of the mullahs, whether they're thousands of peasants bused in to attend religious demonstrations in Tehran or Hezbollah thugs who beat up students. And, not least, the foundations serve as cash cows for their managers.
"It usually works like this," explains this businessman. "Some foreigner comes in, proposes a deal to the foundation head. The big boss says: ‘Fine. I agree. Work out the details with my administrator.' So the foreigner goes to see the administrator, who tells him: ‘You know that we have two economies here--official and unofficial. You have to be part of the unofficial economy if you want to be successful. So, you have to deposit the following amount into the following bank account abroad and then the deal will go forward.'"
Today Rafiqdoost heads up the Noor Foundation, which owns apartment blocks and makes an estimated $200 million importing pharmaceuticals, sugar and construction materials. He is quick to downplay his personal wealth. "I am just a normal person, with normal wealth," he says. Then, striking a Napoleonic pose, he adds: "But if Islam is threatened, I will become big again."
Implication: He has access to a secret reservoir of money that can be tapped when the need arises. That may have been what Ayatollah Rafsanjani had in mind when he declared recently that the Islamic Republic needed to keep large funds in reserve. But who is to determine when Islam is in danger?
As minister of the Revolutionary Guards in the 1980s, Rafiqdoost played a key role in sponsoring Hezbollah in Lebanon--which kidnapped foreigners, hijacked airplanes, set off car bombs, trafficked in heroin and pioneered the use of suicide bombers. According to Gregory Sullivan, spokesman for the Near Eastern Affairs Bureau at the U.S. State Department, the foundations are the perfect vehicles to carry out Iran's shadow foreign policy. Whenever suspicion of complicity in a terrorist incident turns to Iran, the Tehran government has denied involvement. State Department officials suspect that such operations may be sponsored by one of the foundations and semiautonomous units of the Revolutionary Guards.
Iran's foundations are a law unto themselves. The largest "charity" (at least in terms of real estate holdings) is the centuries-old Razavi Foundation, charged with caring for Iran's most revered shrine--the tomb of Reza, the Eighth Shiite Imam, in the northern city of Mashhad. It is run by one of Iran's leading hard-line mullahs, Ayatollah Vaez-Tabasi, who prefers to stay out of the public eye but emerges occasionally to urge death to apostates and other opponents of the clerical regime.
The Razavi Foundation owns vast tracts of urban real estate all across Iran, as well as hotels, factories, farms and quarries. Its assets are impossible to value with any precision, since the foundation has never released an inventory of its holdings, but Iranian economists speak of a net asset value of $15 billion or more. The foundation also receives generous contributions from the millions of pilgrims who visit the Mashhad shrine each year.
What happens to annual revenues estimated in the hundreds of millions--perhaps billions--of dollars? Not all of it goes to cover the maintenance costs of mosques, cemeteries, religious schools and libraries. Over the past decade the foundation has bought new businesses and properties, established investment banks (together with investors from Saudi Arabia and the United Arab Emirates) and financed big foreign trade deals.
The driving force behind the commercialization of the Razavi Foundation is Ayatollah Tabasi's son, Naser, who was put in charge of the Sarakhs Free Trade Zone, on the border with the former Soviet republic of Turkmenistan. In the 1990s the foundation poured hundreds of millions of dollars into this project, funding a rail link between Iran and Turkmenistan, new highways, an international airport, a hotel and office buildings.
Then it all went wrong. In July 2001 Naser Tabasi was dismissed as director of the Free Trade Zone. Two months later he was arrested and charged with fraud in connection with a Dubai-based company called Al-Makasib. The details remain murky, but four months ago the General Court of Tehran acquitted him.
Iran's most distinguished senior clerics are disgusted by the mullahcrats. Ayatollah Taheri, Friday prayer leader of the city of Isfahan, resigned in protest earlier this year. "When I hear that some of the privileged progeny and special people, some of whom even don cloaks and turbans, are competing amongst themselves to amass the most wealth," he said, "I am drenched with the sweat of shame."
Meanwhile the clerical elite has mismanaged the nation into senseless poverty. With 9% of the world's oil and 15% of its natural gas, Iran should be a very rich country. It has a young, educated population and a long tradition of international commerce. But per capita income today is 7% below what it was before the revolution. Iranian economists estimate capital flight (to Dubai and other safe havens) at up to $3 billion a year.
No wonder so many students turn to the streets in protest. The dictatorship has been robbing them of their future.
Discontent Unveiled
Disaffected, denied opportunity and just plain bored, Iran's youth have taken their frustrations with the clerics' regime to the streets.
Paul Klebnikov, The Author of - - Millionaire Mullahs - - Was Shot Dead - Late Friday, July 09, 2004
MOSCOW - - The American editor of Forbes Magazine's Russian edition and author of a book about tycoon Boris Berezovsky was shot to death late Friday, July 09, 2004, the magazine said.
Paul Klebnikov, 41 years old, was shot four times outside the magazine's office and died in a rescue-squad vehicle, Russian news reports said. The radio station Ekho Moskvy said shells of two different caliber were found at the scene, indicating at least two assailants.
Police could not be reached for comment, but the killing was confirmed in a statement by Forbes publisher Steve Forbes.
"Paul was a superb reporter -- courageous, dedicated, ever-curious" the statement said. "He knew Russia well. It was a country he deeply loved."
Alexander Gordeyev, editor of the Russian edition of Newsweek magazine, which has offices in the same building, said he came to Klebnikov's side as he lay outside the building.
He was still conscious and able to speak, "Klebnikov thought that the ruling mullahs in Iran could have been the cause of the attack." Gordeyev told The Associated Press.
The Interfax news agency quoted Leonid Bershidsky, the publisher of Russian Forbes and Newsweek, as saying that Klebnikov recently "had not dug up anything sensitive." Forbes started its Russian-language edition in April. Klebnikov, U.S.-born of Russian heritage, previously had been a senior editor with the U.S.-based Forbes.
In a statement late Friday, Klebnikov's family said it expected Russia to bring the assailants to justice, and urged "U.S. and international authorities" to make sure that happens.
"Paul was a fighter for the truth," the statement said. "Even more, he believed in being positive and looking for ways to make the future better. We mourn his death."
In May, Forbes attracted wide attention by publishing a list of Russia's wealthiest people, claiming that Moscow had more billionaires who worked there or amassed their fortunes there than any other city in the world.
"Here people fly and fall with staggering speed," Klebnikov said at a news conference when the list was released.
His 2000 book "Godfather of the Kremlin: Boris Berezovsky and the Looting of Russia" described how Berezovsky, now living in exile in Britain, allegedly siphoned hundreds of millions of dollars out of Russia.
After Klebnikov wrote a profile of Berezovsky for Forbes in 1996, Berezovsky filed a libel suit against the magazine in Britain.
He withdrew the suit in 2003 after the publication acknowledged it was wrong to allege he was involved in the murder of a television personality.
Klebnikov in May said that he believed the chaotic post-Soviet years, when business disputes were often settled by gunfire and car bombs, were a thing of the past.
"The era of so called bandit-capitalism is already in the past. In the mid-90's it was a very, very dirty process ... I think the participants of our list themselves are pleased to leave this era behind," he said.
Klebnikov was a graduate of the University of California at Berkeley and the London School of Economics.
Communities Fight State Laws That Can Divide Broadband Access

- By EDWARD WYATT - The New York Times - NOV. 9, 2014
Small cities are asking the F.C.C. to use its power to override laws in 19 states that forbid municipalities (the people) to build or expand broadband networks..!
WILSON, N.C. — Jason Bissette could throw a sweet potato from his office here in eastern North Carolina, where he and his family oversee nearly 3,000 acres, to their newest barn.
But despite his wishes, Mr. Bissette cannot extend the high-speed broadband from the office to his barns, either by wire or Wi-Fi, an upgrade that would help him monitor his sweet potatoes and tobacco.
The problem is that his office sits in Wilson County, where a municipal power company has built a high-speed fiber-optic network. The barns, however, sit in Nash County. And a three-year-old state law prohibits the city of Wilson’s utility from expanding its broadband network outside its home territory.
“The technology is right there across the county line,” Mr. Bissette said on a recent afternoon, after plowing up a field of sweet potatoes for harvest. “If we could get the service, we could make sure the temperature is right, that air is circulating. It would make life a whole lot simpler.”
In North Carolina, as in 18 other states, state laws limit municipalities from building or expanding high-speed Internet service networks. The reason behind those laws, supporters say, is to limit taxpayer exposure to projects that at times fail and for which there may be little demand.
But Tom Wheeler, the Federal Communications Commission chairman, says providing access to broadband Internet is in the public interest. And for that reason, he says, the commission can override those state laws — setting off a heated debate about the federal commission’s authority over states and about whether local governments or private companies should provide the service.
Mark Cooper, research director of Consumer Federation of America, said he expected “a long and vicious fight. There is a felt need for a higher quality of service at a more reliable price. There’s a perception of market failure. If consumers were not upset, they wouldn’t be asking for it.”
At the center of the debate are Chattanooga, Tenn., and Wilson. The two cities have petitioned the commission to invalidate their state laws. A ruling from the F.C.C. is expected next year.
In Wilson, which had a population of just under 50,000 in 2013, the municipal power company also provides electricity for six surrounding eastern North Carolina counties. The city told the F.C.C. that numerous residents, government agencies, businesses and other organizations in those counties had requested its high-speed Internet service. But the state law, it said, had “the purpose and effect of prohibiting it” from offering broadband.
Will Aycock, the general manager of Greenlight, Wilson’s broadband service, said that drivers often stopped when they saw Greenlight trucks working outside the city to ask if and when the broadband service would be available in nearby areas.
Inside its current territory, about one-third of the 21,000 households subscribe to Greenlight’s broadband service. Time Warner Cable and CenturyLink also provide broadband to the county, but their services deliver slower speeds and are more expensive.
“We would probably be building tomorrow if the law changed today,” Mr. Aycock said. “We’re not saying that we’re going to build out all of eastern Carolina or even all of our service territory tomorrow. But there are areas where we’d like to go now.”
One of the potential places to expand is Pinetops, a town of 1,300 people about 20 miles northeast of Wilson. Pinetops had already been negotiating with Greenlight for broadband service when the North Carolina law went into effect in 2011.
Pinetops buys electric power from the City of Wilson, which also owns the fiber-optic network. But the main broadband option is through CenturyLink, the large telecommunications company, over the copper-wire phone network, whose speed does not match that of Wilson’s fiber-optic broadband.
“If you want to have economic development in a town like this, you’ve got to have fiber,” said Gregory Bethea, the town administrator of Pinetops. He said that while it was doubtful that the small community would attract a 300-employee factory, it might be a prime location for a call center or other service business that relied on telecommunications.
But CenturyLink says that there is not enough demand in or around Wilson for fiber-to-home broadband.
“We build our network to meet customer expectations,” said Bill Hanchey, a CenturyLink regional vice president who oversees government affairs. But customers are not clamoring for the speed provided by fiber, he said. “It does us no good to go out and build networks that customers don’t need or aren’t requesting.”
Supporters of the North Carolina law say it promotes broadband expansion, as long as private companies are put on a level playing field with public entities — being allowed the same access to telephone poles, for example.
The law is also intended to keep taxpayers from being stuck with a bill for a failing network. In North Carolina, as in many other states, the law says a broadband system cannot be subsidized with revenue from other utilities. North Carolina also requires municipalities to hold a special election to approve such projects. Wilson’s system, which was built before the law, was simply approved by its City Council.
Such elections are not always a hindrance. In Colorado, which has similar requirements, two cities and six counties approved ballot measures this month allowing for local broadband.
Several municipal systems have failed, including those in Burlington, Vt.; Monticello, Minn.; and Dunnellon and Quincy, Fla., according to an extensive report on government-owned broadband by Charles M. Davidson and Michael J. Santorelli, directors of the Advanced Communications Law & Policy Institute at New York Law School. They found that in Provo, Utah, taxpayers were left with $40 million in debt from the construction of a system after it was sold to Google for $1.
In most cities, they say, other infrastructure needs like roads and bridges are more pressing. Broadband “is not where we have the most compelling need for investment,” Mr. Davidson said in an interview. “And when government networks fail, the failure is on the backs of the people.”
But those pushing for community broadband say the level of opposition the systems provoke from cable and phone companies is evidence that they work.
“If the people,” Mr. Wheeler wrote in June, “acting through their elected local governments, want to pursue competitive community broadband, they shouldn’t be stopped by state laws promoted by cable and telephone companies that don’t want that competition.”
That the fight has landed at the F.C.C. is the result of the Telecommunications Act of 1996, in which Congress charged the commission and the states to encourage the deployment of advanced communications capabilities on a reasonable and timely basis. If deployment was found lacking, the commission was empowered to act immediately to remove barriers to infrastructure investment and to promote competition.
For the F.C.C. to invalidate the state law, it will have to overcome a United States Supreme Court precedent that seems to favor the states. In Nixon v. Missouri Municipal League, the Supreme Court ruled 8 to 1 that the Telecommunications Act allowed states to prevent municipalities from providing telecommunications services.
“I am pretty confident that if the F.C.C. pre-empts state laws, they ultimately will lose those cases,” said Randolph J. May, president of the Free State Foundation and a former associate general counsel for the F.C.C. “The Supreme Court jurisprudence is pretty clear.”
The Cities of Wilson and Chattanooga have argued that broadband service is classified as an “information service” and not a “telecommunications service.” That could mean that the Nixon ruling does not apply; instead, at issue is the section of the law that requires the commission to remove barriers to the expansion of broadband.
In the early 20th century, Wilson was the world’s largest bright-leaf tobacco market, and even now the Bissette family’s annual tobacco harvest fills 52 barns — all of them in Nash County, where the municipal broadband cannot go.
“When you’re putting the tobacco in, you need to keep the air circulating,” Mr. Bissette said. “If we could get the broadband over here, we could monitor the tobacco barns. We’d know at any point in the night if there was a problem.”